by our Cyber Threat Intelligence Team

Like all organisations, industrial companies such as manufacturers and utilities are regularly targeted by cyber-attacks. Since they operate Industrial Control Systems (ICS) or Operational Technologies (OT), the consequences of such attacks can be dramatic and far-reaching, including the interruption of essential services like power and water.
Cyber-attacks on industrial companies
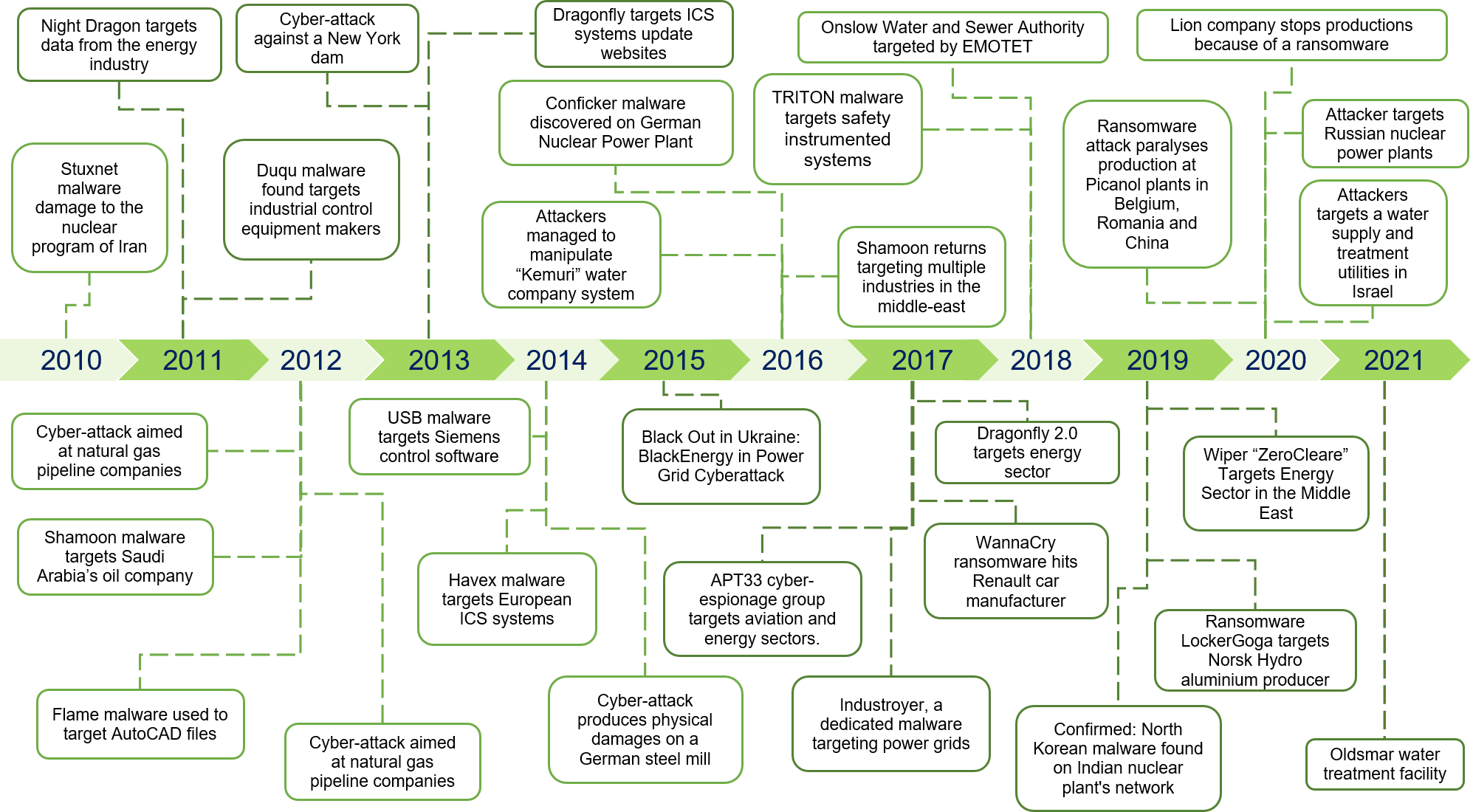
Figure 1: Timeline showing cyber-attacks impacting industrial companies during the last 10 years (not exhaustive)
Ransomware and cybercrime groups
Ransomware-based extortion is currently popular among cybercrime actors. Since their aim is to quickly make money from cyber-attacks, companies with manufacturing activities make for appealing targets. Ransomware often infiltrates a target system through established techniques such as phishing or by exploiting vulnerabilities in external remote services. As the IT network provides those services, it is regularly the first to fall to a ransomware attack.
In March 2019, the aluminium producer Norsk Hydro was hit by the LockerGoga ransomware [1] .This devastating attack cost the firm $71 million [2] and impacted several sites across the globe. While the malware spread, it impacted the industrial network, forcing the company to either shut down its production lines or switch to manual operations [3].
Another example is the beverage manufacturer Lion, [4] which was impacted by the Sodinokibi [5] ransomware in June 2020. After the attack forced the shutdown of its systems for safety reasons on June 9th, it took until June 26th for most operations to get back up and running. Even then, the company’s systems were not operating at the same capacity as they were prior to the attack.
In most cases, ransomware impacts industrial activities while propagating through a network, eventually contaminating windows machines connected to a manufacturer’s production lines. This forces the manufacturer to shut them down for safety reasons (loss of visibility on the production line and loss of control). While directly targeting ICS processes does not appear to be a common ransomware trend, some – like the ransomware Ekans [6] – seem to have elements directly targeting ICS processes.
Advanced Persistent Threat and targeted objectives
Advanced Persistent Threat (APT) groups are often linked to geopolitical objectives. As financial extortion is not their main goal, they aim to achieve specific impacts on the systems they target. Stuxnet and Shamoon are two examples of malware which aimed to destroy their target systems – though both acted differently.
Shamoon
The Shamoon [7] wiper was designed to overwrite data contained on disks and had features targeting the Master Boot Record to make the disks unusable. In August 2012, Saudi Aramco’s company network fell victim to the wiper. As its production network is segregated from the internal communication network, its capacity to extract oil was not impacted. But, as its IT payment system was unavailable, the oil could not be sold. To further embarrass Aramco, the attackers published confidential IT information online, including login credentials [8]. The company networks were still not fully up and running two months after the attack [9]. In a post on PasteBin.com, the attackers, named “Cutting Sword of Justice”, took credit – claiming the attack was a retaliation for the actions of the Al-Saud regime.
Stuxnet
In comparison, the Stuxnet [10] worm was stealthier. Though the worm has been found in various countries, it was mostly active in Iran, where it took out the centrifuges used by the Iranian state to purify uranium, delaying its nuclear research program. It was later discovered that the worm had features allowing it to perform reconnaissance on the infected system, so that it would only activate itself on its target.
Targeting essential utilities
As a steady supply of clean water is vital, water treatment facilities and other utilities are often targeted by cyber-attacks. Last January, the City of Oldsmar in Florida had the dosing rate of Sodium Hydroxide in its water manipulated by an external source [11]. Luckily, the attack was detected by the operator before any water was poisoned. The remote access software TeamViewer served as the attacker’s point of access to the engineering workstation. Though in this case, the security failure was caused by the previous installation of TeamViewer, some malware is specifically tailored to target critical infrastructure systems. One example is Industroyer [12]. While using standard communication protocols, this malware is able to command the switches and circuit breakers of an installation. This can allow it to turn off or damage the system. While not proven, the malware has the necessary functionalities to have caused a power blackout in a part of Kiev in 2016.
Conclusion
Unfortunately, there’s no escaping the fact that industrial companies are going to keep being targeted by increasingly sophisticated cyber-attackers. While most attacks are not focused on ICS and OT, these systems can still be seriously impacted. Moreover, due to their societal importance, the services of utilities and manufacturers are a target of choice for APT groups, and are also on the radar of cybercriminals and ransomware groups around the world.
To find out more about how different industries can be affected by cyber-attacks and how they can defend their infrastructure, take a look at our other articles here.