With global political tensions rising and espionage increasingly moving into the cyber sphere, government bodies are more at risk from hackers than ever before. Ensuring the cyber security of governments and public institutions therefore requires a careful balancing act.
Leaders must prioritise important digital transformation programmes that increase connectivity – such as cloud adoption – alongside strong cyber security measures, all while navigating an increasingly complex regulatory and compliance landscape.
Our approach
In the current digital climate, technology moves at lightning speed and cyber criminals move even faster. To stay one step ahead, we draw on our innovation pedigree and Airbus DNA.
Having safeguarded Airbus’ complex systems and networks for over three decades, we now also protect the networks, data and services of various government institutions. For instance, since 2017, we have worked with key EU institutions as part of Europe’s most important cyber framework contract.
Our approach is based on an ethos of continuous cyber security maturity improvement. We can support you every step of the way, from uncovering the vulnerabilities in your systems, to designing, implementing and maintaining a solution that can defend against the most advanced threats.


“What makes us different from other players is the fact that we work with complex networks and the most sensitive data, from defence and governments to Airbus and other CNI. Our industrial roots give us a unique understanding of the challenges faced by our customers. We are also the only company with a sovereign presence in France, Germany, the UK and Spain.”
Which solution is right for you?


Identify
Our cyber security consulting services help governments and public institutions identify how to boost their cyber maturity and comply with current and future regulations.
In addition, we offer a range of cyber security simulation and training services, tailored to multiple audiences – from technical experts to operational managers.


Protect
Ensure your systems are always protected with our market leading network segregation, trusted infrastructure, system integration and identity management solutions and services. These include:
- Architecture, design and integration services
- High grade encryption
- Secure key management
- Secure gateways
- Identity access management and single sign-on solutions


Detect
Uncover hidden vulnerabilities and detect system intrusions with our comprehensive range of detection products and services, including:
- Security Operations Centres (SOC)
- Cymerius incident response tool
- Orion Malware analysis
- Digital risk protection solutions


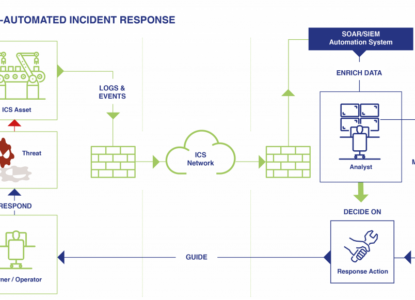
Respond
A breach of your IT systems can have serious real-world consequences, particularly if your institution handles highly sensitive data. We can help your teams prepare for an attack with cyber crisis management exercises and penetration testing, as well as support you during incident response and recovery.